Researchers from Ben Gurion University successfully executed a hack on a 3D printing process, but I’m wondering what to make of it.
The research was documented in a short video that explains the steps undertaken:
- A hacker introduces malware via a phishing attack to a victim whose PC holds certain STL 3D models
- The malware connects remotely to the hacker and enables control of the PC’s files
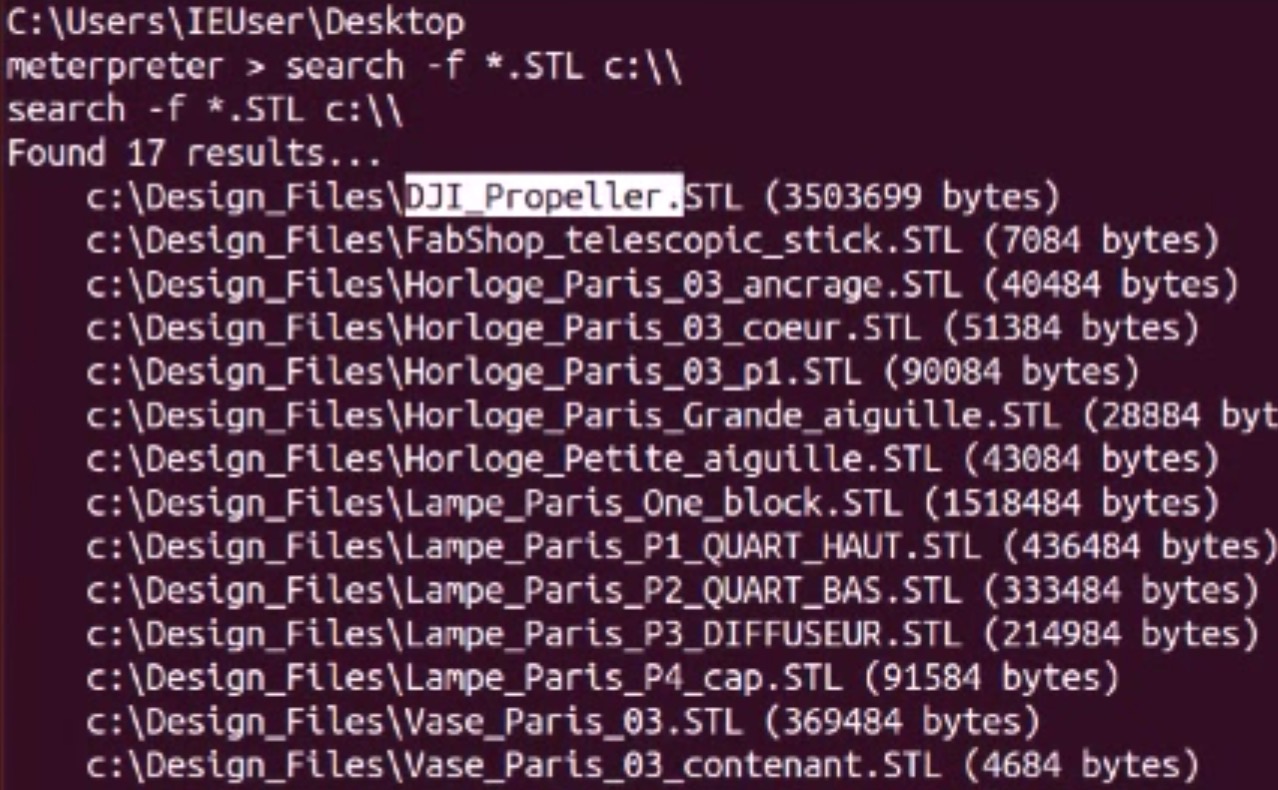
- The hacker downloads a specific 3D model, in this case a propeller model
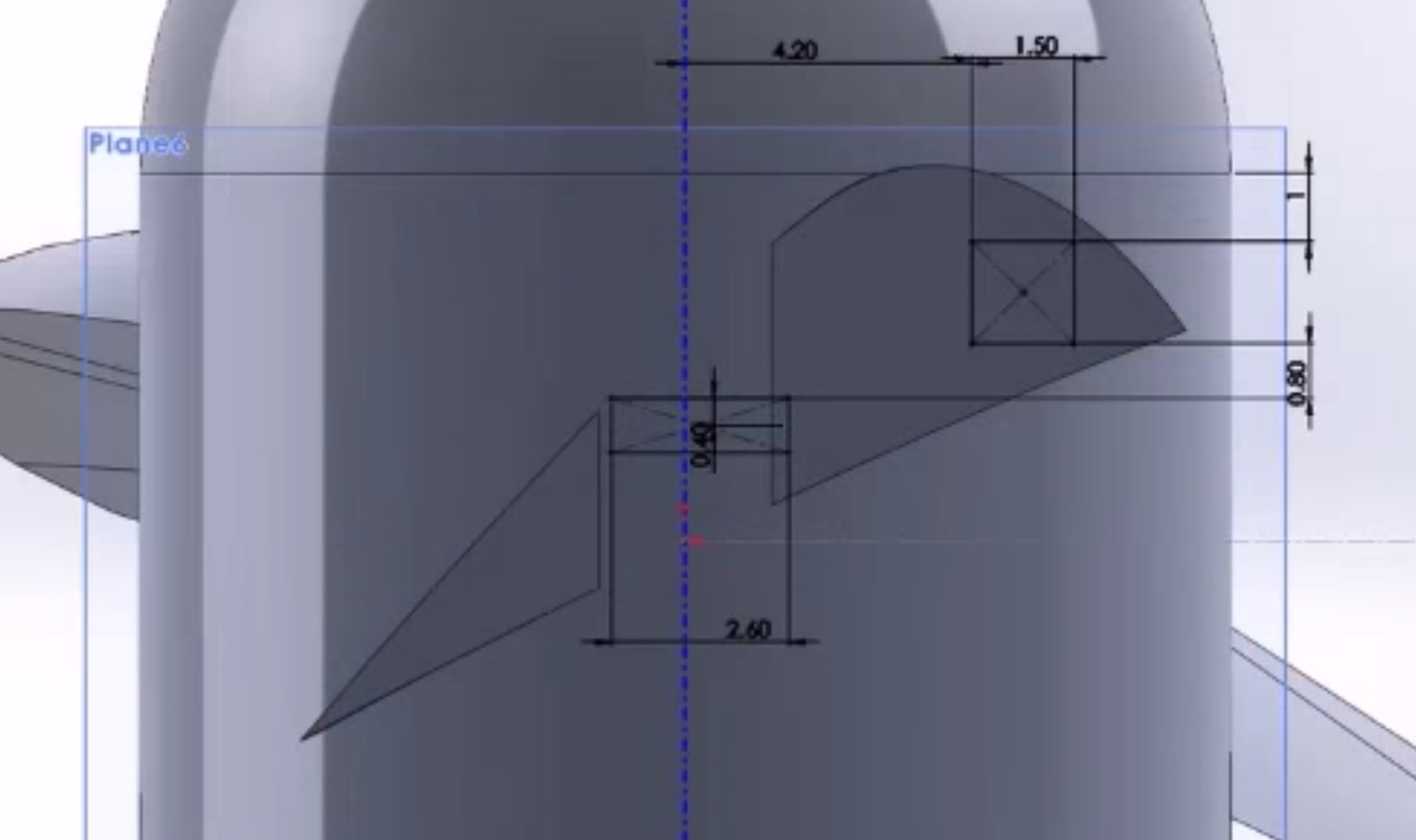
- The hacker then uses a CAD system to “adjust” the 3D model by introducing “cavities” in the propellor’s interior that would dramatically weaken the object, yet not be visible externally
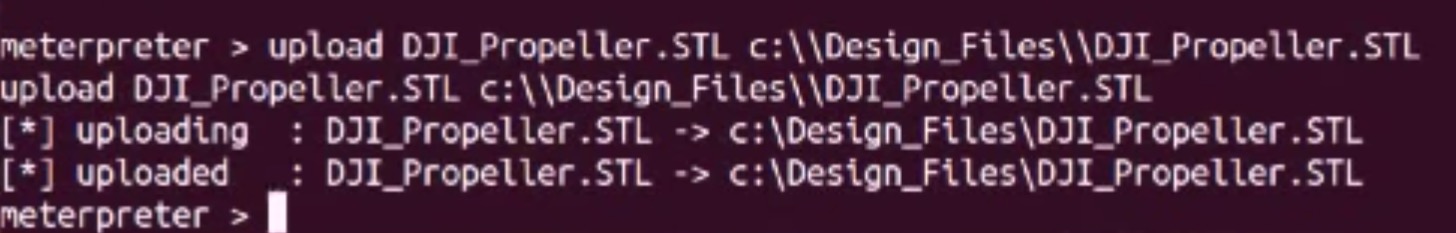
- The updated STL files are uploaded to replace the original files on the PC
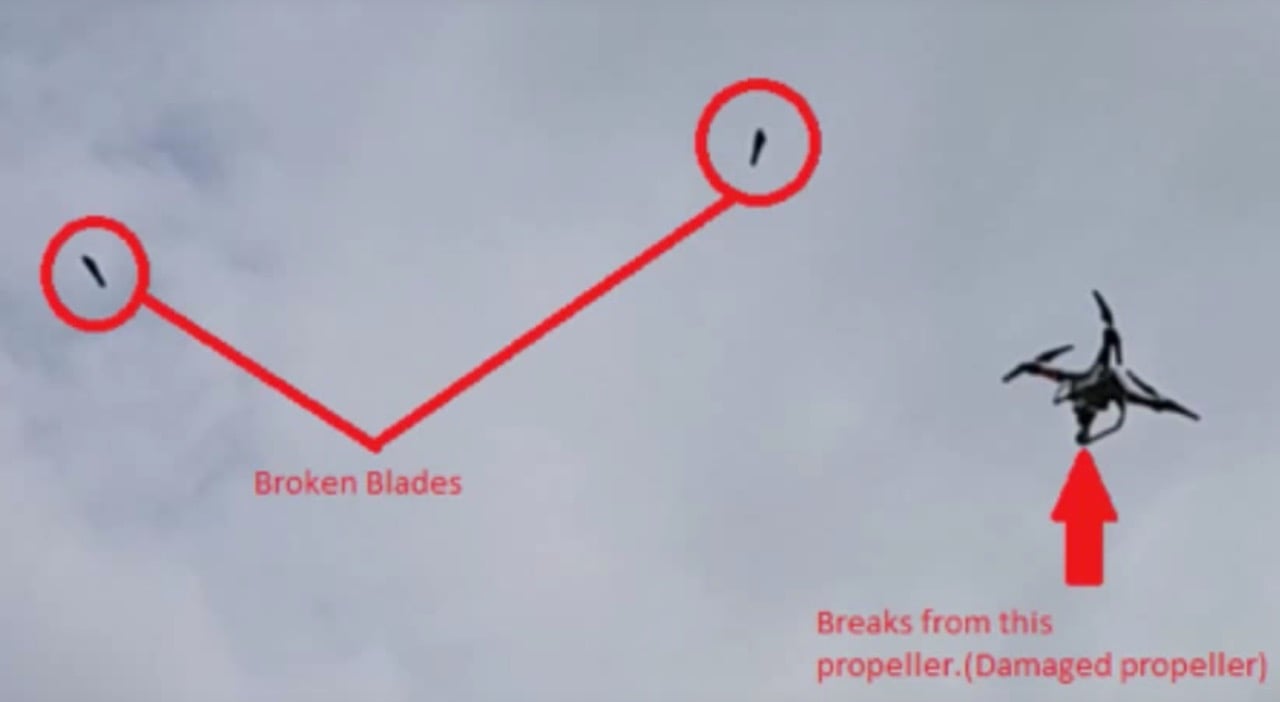
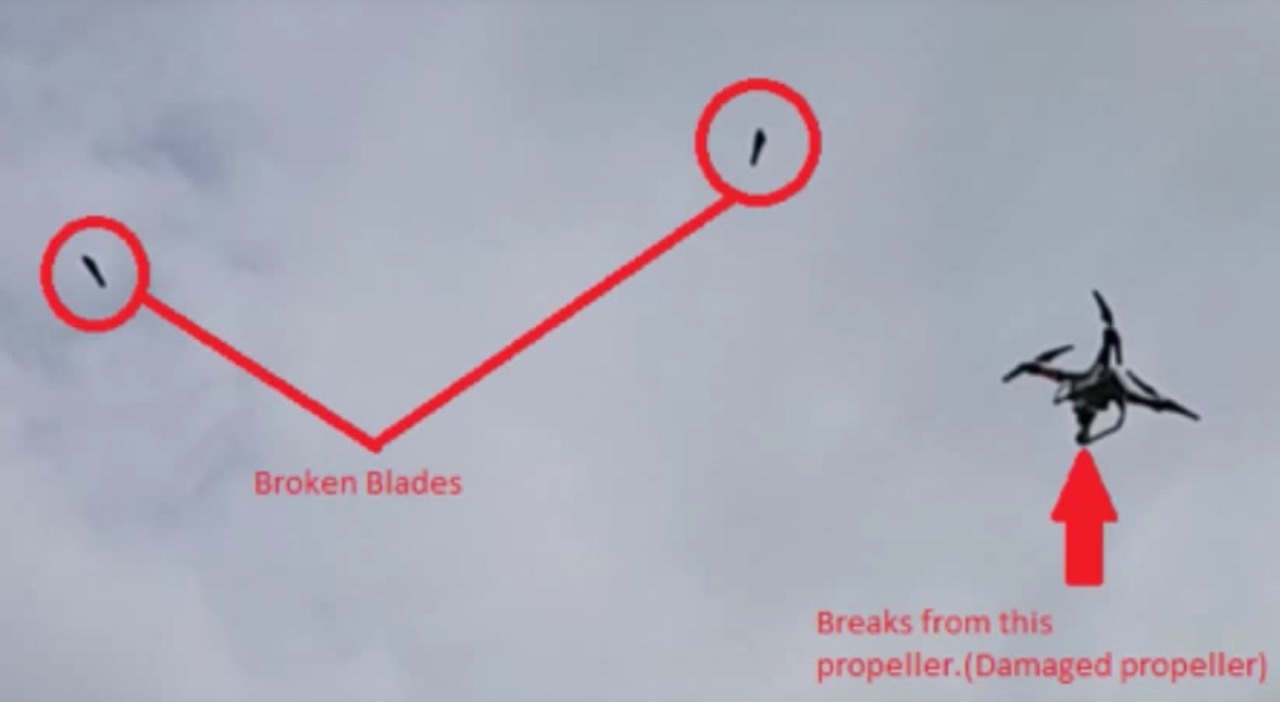
- The unknowing user 3D prints the propeller and gets a nasty surprise when flying the drone with it
Here’s the whole video:
This approach would certainly work in this particular scenario, but I’m a bit mystified why it would be feasible in real life.
Anyone designing a serious part would want to provide protection for their design files, particularly in large companies. The designs are literally more important than the parts themselves!
Parts are very often versioned, with multiple iterations occurring to eventually arrive at a final design. These iterations should be tracked using a version control system, and indeed often are, again especially in large companies. Such an attack would be much more complex if the 3D model is embedded within a cloud-based (or local network) management system, and it would be subject to audit logs detailing a change.
To me, an STL file is simply yet another digital document that should be protected, just like all the other files you make use of. If you’re compromised, then ALL of your files are questionable, be they database, email, images, audio, documents or yes, even 3D models. This is not a surprise to me; someone breaks in and messes up your files.
Don’t let them break in.
Manage your 3D files.
It just makes sense.