 We’re always interested in ways to develop 3D models for printing, and this method is quite startling: Teleduplicating physical keys via optical decoding!
We’re always interested in ways to develop 3D models for printing, and this method is quite startling: Teleduplicating physical keys via optical decoding! Yes, they take a picture of your keys and then using sophisticated image analysis techniques can prepare a 3D model that duplicates the key shape. It’s, called, obviously, “Sneakey”.
In the top image (click for larger view) the keys were photographed from almost 200 feet away (from a spy position on the rooftop of a 4 story building). The theory was that a security attack could take place remotely without the victim being aware of the theft. The experiment proved conclusively that this could be done, even when the key is positioned at various angles.
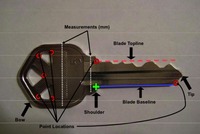 The software, written in Matlab, analyzes the image and produces the codes corresponding to the key shape. Then these codes could be used on a code cutting to produce an actual usable metal key.
The software, written in Matlab, analyzes the image and produces the codes corresponding to the key shape. Then these codes could be used on a code cutting to produce an actual usable metal key. But we think these codes could also be fed into software that would convert them into a solid 3D model suitable for 3D printing. And then everyone can print keys.
What will the world be like when anything you see can be duplicated?


the little picture of the key kinda looked like a jetski on facebook.. very dissapointed.
jk, this is seriously scary. Open your door with an sms i say.
the little picture of the key kinda looked like a helicopter on facebook. clicking on this to discover some spy story which doesn't involve mini key like helicopters has been dissapointing to say the least….
To the "Keyskin" comment – that sounds akin to the "Faraday wallets" to protect RFID enhanced credit cards and IDs. It does sound like a good idea, but the other thing is – when do you ever have your keys just laying about? At home maybe, but I always have my keys either in my pocket or in my desk drawer. It's just another level of vigilance to protect ourselves in this new era of technology.
Obvious solution: a "Keyskin," a foam rubber cylinder that fits over the key and compresses when the key is pushed against a keyhole so the key can work.
If you have access to a 3D-Printer and OpenSCAD then you can just print the key using those key codes.
http://eclecti.cc/hardware/physical-keygen-duplicating-house-keys-on-a-3d-printer
No key is safe!