Charles Goulding and Lara Tomiko of R&D Tax Savers discuss cyber security concerns in 3D printing.
The 3D printing product business is typically comprised of vendors that sell 3D printers, materials and software. Increasingly the prospective purchasers of these products will not approve of a new 3D printed products vendor until that vendor demonstrates that they have a comprehensive cyber security policy, including specific employees with designated cyber security internal control duties. Similar to employee hiring verification, many purchasers use a third party organization to review and verify cyber security compliance. This means aspiring 3D printed products vendors not only need to have current cyber security policies, but they should also be expected to provide additional confirmation of those policies when asked, including testing and formal auditing for larger relationships.
Although establishing these internal cyber security control procedures for the first time may seem costly and foreboding, once a good program is established it will serve to demonstrate compliance with the increasing number of 3D product purchasers requiring this type of compliance. Vendors with established programs will be able to distinguish themselves and capture 3D product orders that require immediate fulfillment since verifying cyber compliance can take weeks and even months. Once a 3D printed product vendor demonstrates compliance with one of the major third party cyber risk verifiers, obtaining new clearances for new 3D product purchasers using the same third party verifier should be much easier.
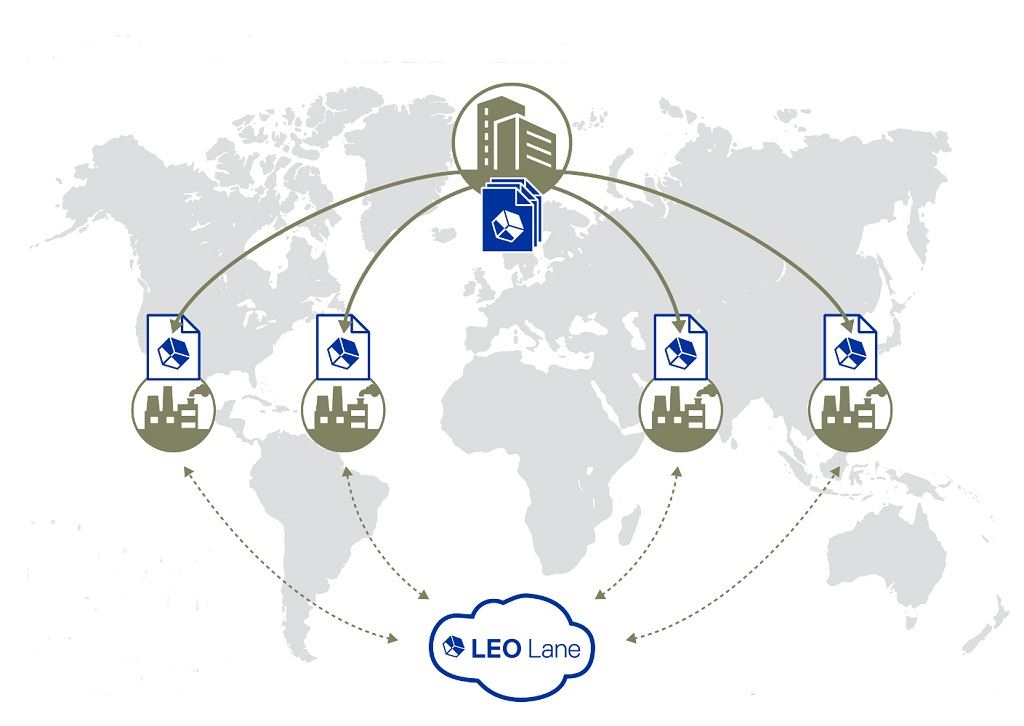
After 3D product vendors establish their own cyber security compliance program, they should institute a similar vendor cyber security program for their own suppliers. Some OEMs mandate that Tier 1 suppliers install mirror cyber risk control policies with their next tier suppliers. It is only by having linked cyber security programs that an industry can be confident that it has a complete cyber security supply chain. Vendors are typically put into different risk assessment categories such as high risk, medium risk and low risk depending on the nature of their interface with the supplier. The greater the data security risk, the greater the required level of cyber security risk controls.
Cyber Security Policy Elements
Some typical cyber security program elements are:
1. Anti-virus solutions
2. Encrypted hard disk
3. Unique and named identity while logging into desktops and laptops
4. A password policy that supports complex passwords and verifies aging and reuse
5. Prohibits excel spread processes on personal device
6. Requires reporting of misplaced or stolen laptop/desktop with excel worksheet
7. Requires reporting of a data breach
Conclusion
It is challenging enough for 3D product vendors to develop create new products and create customer demand for those products. After finally attracting customer interest it might be frustrating to then confront additional administrative compliance burdens. However in today’s technology world cyber security is major risk and those 3D product vendors who manage this risk will improve their success rate.








Create It REAL has signed a deal with Spentys to help devise a secure system that provides onsite 3D printing of orthopedic devices in practice offices.